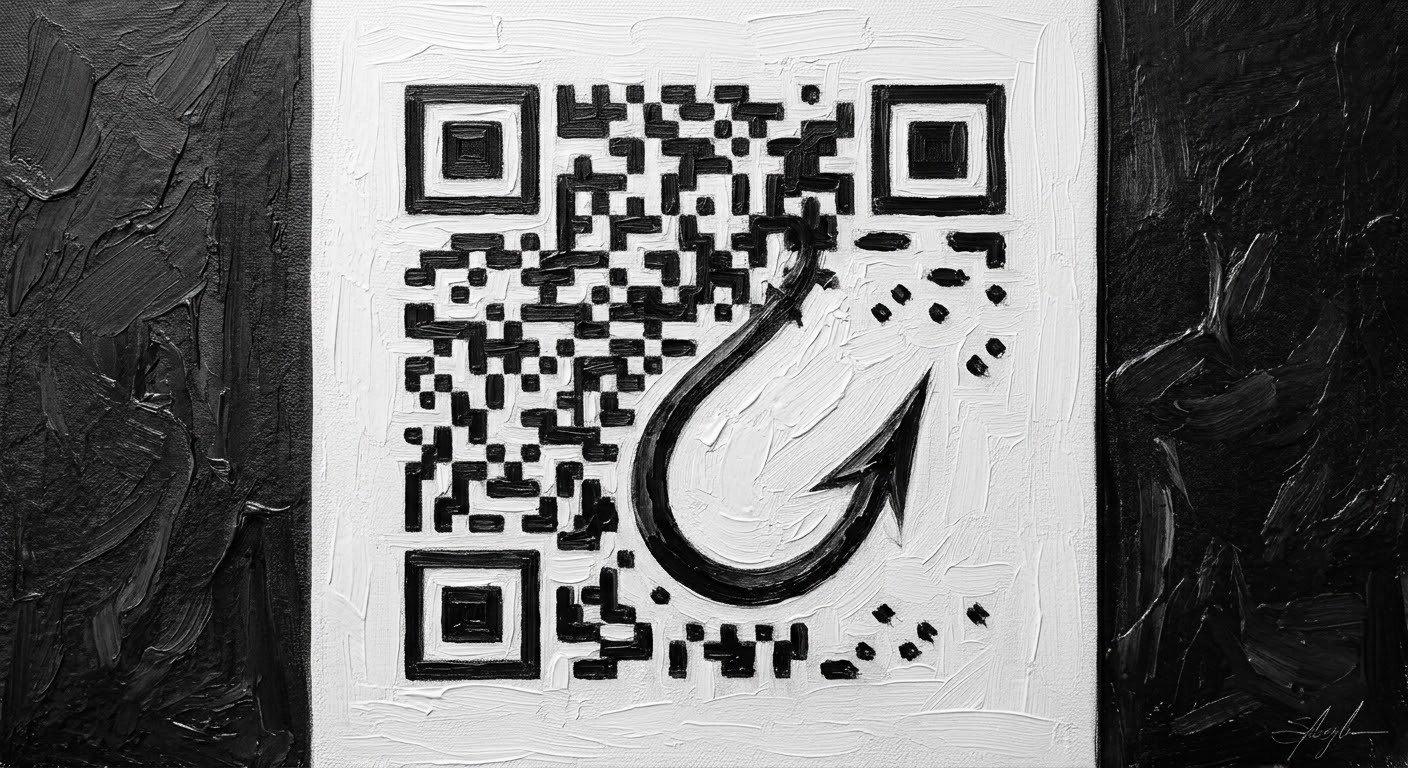
TL;DR: A threat actor ran a three-wave QR code phishing campaign that bypassed every email control - SPF, DKIM, DMARC, and Microsoft Defender - delivering 28 emails to inboxes undetected. Here's what happened and what to do about it.
-
The attack encoded phishing URLs inside BMP image attachments, making them structurally invisible to text-scanning email security tools - execution happened on mobile devices, outside corporate endpoint controls
-
Each recipient received a uniquely generated QR code with a distinct file hash, defeating IOC sharing; the attacker's tracking ID system suggests over 1.6 million emails were sent to other organizations in parallel
-
7AI's AI SOC agents identified the true positive, PLAID ELITE analysts confirmed the mechanism, and a targeted threat hunt mapped the full campaign - turning one alert into actionable intelligence across all three waves
|
TLP: WHITE - For Public Distribution. All customer and organizational identifiers have been anonymized. IOCs in this report are confirmed from active investigations and public research. Defenders are encouraged to share and operationalize these indicators. |
“This started out looking like a fairly standard phishing case, but with each hunt and discovery, it became clear the attack was far more sophisticated. The emails passed SPF, DKIM, and DMARC, contained no visible links, and used QR codes in image attachments to deliver the payload. With per-recipient tracking, multi-wave delivery, and reconnaissance through auto-replies, what began as a single alert quickly revealed a coordinated campaign.”
Juliana Testa
7AI Threat Research Team
Executive Summary
Over a 20-day period, a threat actor identified by 7AI conducted a multi-wave QR code phishing campaign against a large enterprise, while targeting many others in parallel. Tracking data suggests the campaign scaled significantly, with over 1.6 million emails sent between waves to other organizations. In this environment, 33 emails were sent to 32 unique recipients across three waves
Of those emails, 28 were delivered directly to inboxes. Zero were blocked, and no automated remediation occurred.
This campaign stood out due to its layered evasion. The attacker’s domain passed SPF, DKIM, and DMARC authentication, and Microsoft Defender assigned a low spam score (SCL 1). No malicious links appeared in the email body. Instead, the emails contained QR codes embedded in image attachments. When scanned, these codes directed users to attacker-controlled URLs where the phishing payload was hosted. Each QR code and payload was uniquely generated per recipient, bypassing traditional detection methods.
7AI’s AI SOC agents escalated the initial alert, and the 7AI PLAID ELITE team initiated a targeted threat hunt. What began as a single detection expanded into a full campaign investigation, uncovering all waves, affected users, and attacker tradecraft.
“From a CISO perspective, the operating model benefit is that an AI agent turns alert investigation from a labor-intensive, tool-hopping process into a fast, consistent, and scalable control that applies expert-level triage to every case, s. It can automatically inspect hidden artifacts such as URLs embedded in QR images, correlate them with identity, endpoint, email, network, and SaaS activity, and produce an evidence-backed narrative that lets the SOC act with higher confidence. The result is better fidelity, less analyst time spent on repetitive enrichment, broader coverage across more alerts, and a stronger ability to contain real threats quickly without having to grow headcount linearly with alert volume.”
This post breaks down how the attack worked, why it was effective, and how to defend against it.
Background: The Quishing Blind Spot
QR code phishing, commonly called “quishing,” is not new. However, its adoption by threat actors has accelerated while many defenses have not kept pace.
The core issue is architectural. Email security platforms are designed to detect malicious links by analyzing text-based content. They scan URLs in the email body, decode HTML, and detonate links in controlled environments. This approach is effective when phishing relies on visible hyperlinks. It breaks down when the link is embedded inside an image.
In this campaign, the phishing URL was never present as text. Instead, it was encoded within a QR code embedded in a BMP image attachment. Because link-scanning engines operate on text and not image data, the malicious URL passed through inspection without detection. Unless a security solution is explicitly configured to extract and decode QR codes from attachments, the underlying URL remains invisible to traditional controls.
The second layer of evasion occurs at the moment of user interaction. When a recipient scans a QR code, they typically use a mobile device. These devices often lack the same protections as corporate workstations, such as endpoint detection, proxy routing, or URL filtering. This shifts execution to a less-monitored surface.
This campaign is a strong example of how these techniques combine. The attacker encoded URLs inside QR code images, delivered them through emails that passed SPF, DKIM, and DMARC authentication, and ensured each QR code was uniquely generated per recipient. This prevented hash-based detection and enabled the campaign to operate at scale.
The result is not a failure of individual controls, but a gap between how defenses are designed to operate and how modern phishing campaigns are executed.
7AI addresses this blind spot by analyzing QR code content within email attachments, extracting the embedded URLs, and correlating them with broader threat signals. This enables detection of phishing activity that would otherwise bypass traditional link-based inspection and provides analysts with visibility into attack paths that extend beyond the email itself.
Campaign Overview
|
Attribute |
Detail |
|
Attacker alias |
Baron Lester |
|
Attacker email |
covid_info@iconicdecipher[.]com |
|
Attacker domain |
iconicdecipher[.]com |
|
Attack technique |
QR Code Phishing (Quishing) - T1566.001 |
|
Lure theme |
COVID-19 / RSV antiviral research PDF |
|
Campaign window |
Feb 26, 2026 - Mar 18, 2026 (20 days) |
|
Total emails sent |
33 |
|
Unique recipients |
32 |
|
Delivered to inbox |
28 |
|
Junked |
5 |
|
Blocked |
0 |
|
Post-delivery remediation |
None - emails remained in inboxes at time of discovery |
Attack Timeline
|
Wave |
Date / Time (UTC) |
Recipients |
Notes |
|
Wave 1 |
Feb 26, 16:01-16:08 |
7 |
PDF variant 1c. Manual or low-rate delivery. |
|
Wave 2 |
Mar 17, 15:00-16:34 |
25 emails / 24 recipients |
PDF variant 1b. Automated burst delivery at 1-2 minute intervals over 94 minutes. One recipient targeted twice. |
|
Wave 3 |
Mar 18, 14:01 |
1 |
PDF variant 1j. Single targeted follow-up. |
The 19-day gap between Wave 1 and Wave 2 is significant. Based on tracking ID analysis (detailed below), the attacker was actively sending to other organizations throughout this period. The target environment was one of many in an ongoing, large-scale campaign.
Technical Analysis
The QR Code Bypass
The attack chain is straightforward and deliberately avoids standard detection points:
- The attacker crafts a personalized email with a unique numeric tracking ID embedded in both the subject line and the phishing URL query parameter.
- The email includes a BMP image attachment containing a QR code. The phishing URL is encoded within the image itself, not present as text in the email body.
- The email passes SPF, DKIM, and DMARC authentication. Microsoft Exchange Online Protection assigns a low Spam Confidence Level (SCL 1), and the message is delivered directly to the inbox without being flagged.
- The recipient scans the QR code using a mobile device. This interaction occurs outside corporate security controls, with no proxy inspection, endpoint agent visibility, or URL scanning.
- The user is directed to an attacker-controlled URL hosting a phishing PDF on the domain iconicdecipher[.]com.
- In some cases, user mailbox auto-replies confirm delivery and account activity back to the attacker, providing reconnaissance value.
The lure itself was a relevant research proposal, written in professional and credible language under the name “Baron Lester.” It asked recipients to review a PDF and optionally share it with colleagues. The social engineering was intentionally low-friction. There was no urgency, no credential harvesting prompt, and no overt indicators of compromise. Just a QR code to scan.
|
Why This Bypasses Traditional Email Security Email link-scanning engines operate on text content and HTML. They cannot read URLs encoded inside image pixel data. Unless a platform is specifically configured to decode QR codes in attachments and detonate the resulting URL in a sandbox, QR code phishing is structurally invisible to traditional email security. Mobile devices, which lack the endpoint controls of a corporate workstation, are where the malicious link is actually triggered. |
Email Authentication: Why It Passed All Checks
The attacker invested in proper DNS configuration. All three standard email authentication mechanisms passed, and Microsoft assigned the highest trust rating available:
|
Check |
Result |
Detail |
|
SPF |
Pass |
198.54.115.2 explicitly authorized as sender for iconicdecipher[.]com |
|
DKIM |
Pass |
Valid RSA-SHA256 signature, d=iconicdecipher[.]com |
|
DMARC |
Pass |
Policy: none - no quarantine or reject enforcement |
|
Microsoft EOP Composite |
Pass |
reason=100 (fully trusted) - SCL 1 assigned, delivered to inbox |
The DMARC policy of none is a detail worth flagging: even if DMARC had detected a problem, no enforcement would have occurred. The attacker did not need to defeat authentication - they configured their domain to pass it legitimately. The email client fingerprint identified in message headers was Microsoft CDO for Windows 2000, a legacy COM automation library commonly embedded in scripted phishing frameworks.
Sending Infrastructure
|
Layer |
Host |
IP |
Notes |
|
Mail relay |
server182.web-hosting.com |
198.54.115.2 |
Namecheap shared hosting - also hosts iconicdecipher[.]com |
|
Delivery |
Microsoft EOP |
- |
Microsoft Exchange Online Protection |
The attacker sends email from a residential Verizon FiOS connection, authenticating through a Namecheap shared hosting account that also hosts the attacker's phishing domain. The SMTP HELO hostname most likely reflects the attacker's own machine name or a compromised machine used as an attack vector.
Per-Victim Tracking and Hash Evasion
Each email contained a unique numeric tracking ID embedded in both the subject line and the phishing URL query parameter:
https://iconicdecipher[.]com/c19_idea/<PDF_VARIANT>.pdf?pdf=<TRACKING_ID>_sd
Critically, each recipient also received a uniquely generated QR code BMP file with a distinct SHA256 hash. This serves two purposes for the attacker:
- Delivery confirmation: when a recipient auto-replies or scans the code, the tracking ID correlates the activity back to a specific target.
- Hash evasion: because every QR code BMP is unique, no single file hash can be used as a blocking indicator across the campaign. Hash-based IOC sharing is structurally ineffective against this technique. Domain and URL-based blocking is required.
Auto-Reply Reconnaissance
One recipient had an active out-of-office auto-reply configured. That auto-reply was successfully delivered to the attacker's inbox at covid_info@iconicdecipher[.]com, confirming to the attacker that the mailbox was active, the email was received, and a real person was behind the address.
This occurred because an Exchange Transport Rule in the organization allowed the auto-reply to bypass outbound filtering for internal-domain email addresses. The rule was doing its intended job - but that intent did not account for the scenario where an external attacker receives the outbound reply.
A second auto-reply from a different recipient was blocked before reaching the attacker.
|
Operational Risk Auto-reply confirmation is not a minor data point for an attacker. A confirmed active inbox is a higher-value target for follow-on spearphishing. Any recipient whose out-of-office response reached the attacker should be treated as elevated-risk and monitored for subsequent targeted attempts. Review outbound auto-reply rules carefully: they should not deliver confirmations to external senders from untrusted domains. |
Manager Targeting and Organizational Enumeration
A notable pattern emerged in the targeting sequence. In Wave 1, the attacker sent emails to a small set of recipients - one of whom was a manager. In Wave 2, 19 days later, the attacker targeted that manager's direct reports.
This pattern is consistent with organizational enumeration via LinkedIn, public directories, or auto-reply responses that reveal organizational context. Wave 1 may have functioned partly as reconnaissance - probing for active mailboxes and directory relationships - in preparation for the larger Wave 2 burst.
Campaign Scale: One Organization Among Many
The attacker's tracking ID system reveals something important about the campaign's overall scale. Between Wave 1 and Wave 2, the tracking ID counter advanced by over 1.6 million IDs. Between Wave 2 and Wave 3, it advanced by approximately 77,000 more.
|
Wave |
Tracking ID Range |
Gap from Prior Wave |
|
Wave 1 |
128,775,671 - 128,776,097 |
- |
|
Wave 2 |
130,417,180 - 130,422,815 |
+1,641,083 IDs in 19 days |
|
Wave 3 |
130,500,062 |
+77,247 IDs in 1 day |
A gap of 1.6 million tracking IDs in 19 days indicates the attacker sent a massive volume of emails to other organizations between the Wave 1 and Wave 2 hits on this environment. This is not a targeted campaign against a single organization. It is a high-volume, industrialized operation. Any organization in a similar sector or profile should treat these IOCs as actively relevant.
How 7AI Detected Quishing at Scale
The detection story here is not a technology story. It is a story about what happens when AI-driven triage, expert human analysis, and proactive threat hunting operate as a connected loop - each step revealing what the one before it could not see alone.
Step 1: Platform Triage - AI Identifies a True Positive
During routine monitoring, the 7AI platform flagged an inbound email as requiring further human review and escalated it accordingly. The platform's AI agents correlated the email headers, attachment type, and sender domain against environmental baselines and determined the alert was a true positive - not noise to be dismissed, but a genuine signal that warranted analyst attention.
.png?width=3042&height=1450&name=image%20(11).png)
That determination matters. Most security teams operate under alert fatigue: high volumes of low-fidelity signals that erode confidence in any individual finding. The 7AI platform's accurate true positive classification is what ensured a human analyst engaged with the right alert at the right time.
Step 2: PLAID ELITE Analyst Confirms and Escalates
A 7AI PLAID ELITE analyst received the escalation and conducted a deeper review. Examining both the email content and the BMP attachment, the analyst confirmed the phishing nature of the email - including the QR code delivery mechanism and the attacker-controlled domain embedded within it. The finding was confirmed as malicious and escalated for broader investigation.
This is the human step that rules-based systems cannot replicate: an analyst with the context to understand what they are looking at, and the judgment to know that a single confirmed phishing email in an organization's mail environment is rarely the whole picture.
Step 3: Security Engineer + Threat Hunt Reveals the Campaign
Working in collaboration with a 7AI AI Security Engineer, the analyst conducted a targeted threat hunt across the email environment. What that hunt uncovered changed the nature of the incident entirely.
The single suspicious email was not an isolated event. It was one delivery in a coordinated, multi-wave campaign: 33 emails sent to 32 unique recipients over 20 days, across three distinct waves, with per-victim tracking infrastructure, scripted delivery, and active reconnaissance against the organization's own mail responses. The attacker had phished across the environment for three weeks before the campaign was fully visible.
Without the threat hunt, the organization would have known about one phishing email. With it, they received a complete campaign map: every targeted recipient, every delivery confirmation, the full attacker infrastructure, evidence of auto-reply reconnaissance, and a prioritized list of remediation actions - including which specific emails to purge by message ID, which domains and IPs to block, and which Exchange transport rules to audit.
|
Three Layers, One Outcome This investigation succeeded because three things worked together: the platform identified a true positive accurately, eliminating the false positive noise that causes teams to miss real signals. The PLAID ELITE analyst applied human judgment to confirm and escalate. And the threat hunt expanded the scope from one email to a full campaign - turning a single alert into an actionable intelligence picture. Remove any one of those layers and the outcome is materially worse. |
Why This Is Hard Without the Right Coverage
The investigation required correlating email delivery records across a 20-day window, identifying per-recipient tracking patterns across 33 messages, extracting per-file metadata from unique QR code attachments, cross-referencing sending infrastructure against threat intelligence, and identifying the auto-reply leakage through mail flow logs. Doing this manually, starting from a single alert, would take hours - and most security teams would not have the available bandwidth to pursue it at that depth, especially when the alert itself initially looks like a single low-severity phishing email.
The combination of AI-driven triage, dedicated expert analysts, and structured threat hunting capability is what made the full scope of this campaign visible in time to act on it.
MITRE ATT&CK Mapping
|
Technique ID |
Name |
Observed in This Campaign |
|
T1566.001 |
Phishing: Spearphishing Attachment |
QR code BMP file attached to email; URL embedded in image data, not body text |
|
T1566.002 |
Phishing: Spearphishing Link |
Malicious URL encoded in QR code; victim redirected to attacker-controlled PDF |
|
T1036 |
Masquerading |
Legitimate display name, passing SPF / DKIM / DMARC; no threat signals raised by email security |
|
T1204.001 |
User Execution: Malicious Link |
Victim must physically scan QR code - execution requires user action on mobile device |
|
T1598 |
Phishing for Information |
Research-themed lure; auto-reply reconnaissance confirmed active mailboxes to attacker |
|
T1587.004 |
Develop Capabilities: Exploits (Email) |
Per-victim unique QR code BMP files with distinct SHA256 hashes; hash-based IOC blocking structurally ineffective |
Indicators of Compromise
Note: Brackets have been added to domain names to prevent accidental resolution. Each recipient in the campaign received a uniquely generated QR code BMP with a distinct SHA256 hash - per-file hash blocking is not effective. Block at the domain and IP level.
|
Type |
Category |
Value / Pattern |
Recommended Action |
|
Phishing Domain |
Malicious Domain |
iconicdecipher[.]com |
Block at DNS resolver, perimeter firewall, and proxy |
|
Sender Address |
Malicious Email |
covid_info@iconicdecipher[.]com |
Block sender in email gateway / tenant block list |
|
Attacker IP |
Malicious IP |
71.105.63.133 |
Block in connection filter / deny list (EOP) |
|
Mail Relay IP |
Infrastructure IP |
198.54.115.2 |
Block at perimeter firewall; query DNS logs for resolution history |
|
Mail Relay Host |
Infrastructure Host |
server182.web-hosting.com |
Block at DNS resolver |
|
Phishing URL Pattern |
Malicious URL |
iconicdecipher[.]com/c19_idea/*.pdf?pdf=*_sd |
Block domain and URL pattern at web proxy; wildcard match on domain |
|
X-Mailer Header |
Detection Signal |
Microsoft CDO for Windows 2000 |
Alert on inbound emails with this X-Mailer value from external senders |
|
QR Code File Type |
Behavioral Signal |
Inbound BMP image attachment from external sender + no URL in body |
Alert / sandbox BMP attachments from external unknown senders |
Detection and Response Guidance
Immediate Actions for Security Teams
- Block iconicdecipher[.]com at your DNS resolver, perimeter firewall, and web proxy. Query DNS logs for any historical resolution of this domain across your environment.
- Block the sender address covid_info@iconicdecipher[.]com and attacker IP 71.105.63.133 in your email gateway tenant block lists and EOP connection filters.
- Purge delivered emails via Microsoft Defender. Use Search & Purge in the M365 Defender portal with the IOC domain and sender to identify and soft-delete any delivered messages. Do not rely on users to delete them manually - they may have already scanned the QR code.
- Identify and notify affected recipients. Contact anyone who received the email, advise them not to scan the QR code if they have not, and ask whether they already did. Any recipient who scanned the code on a mobile device should be treated as higher-risk and followed up for potential credential compromise.
- Check for auto-reply leakage. Review outbound mail logs for any auto-replies or out-of-office responses delivered to addresses at iconicdecipher[.]com or 71.105.63.133. Any mailbox that confirmed delivery to the attacker is an elevated-risk target for follow-on spearphishing.
- Review outbound auto-reply transport rules. Audit Exchange transport rules that allow auto-replies to bypass outbound filtering. Rules allowing auto-replies to external recipients should be evaluated for whether they should apply to domains not in a trusted partner list.
Detection Rules
The following behavioral patterns are high-fidelity detection signals for this campaign and for quishing attacks more broadly:
|
Signal |
Logic / Pattern |
|
Inbound BMP attachment from unknown external sender |
email.attachment.extension = 'bmp' AND email.sender.domain NOT IN trusted_domains AND email.direction = 'inbound' |
|
BMP attachment with no URL in body (quishing indicator) |
email.has_attachment = 'bmp' AND email.body_url_count = 0 AND email.direction = 'inbound' |
|
X-Mailer: Microsoft CDO for Windows 2000 (scripted sender) |
email.header.x_mailer CONTAINS 'CDO for Windows 2000' |
|
Outbound auto-reply to unrecognized external domain |
email.direction = 'outbound' AND email.subject CONTAINS 'Out of Office' AND email.recipient.domain NOT IN trusted_partner_domains |
Long-Term Recommendations
- Enable QR code scanning in Microsoft Defender for Office 365. Microsoft Defender has a feature to decode QR codes embedded in emails and attachments and detonate the resulting URLs. Verify this is enabled in your anti-phishing policies. This is the single most effective technical control against this attack vector.
- Enforce DMARC with a quarantine or reject policy on your own domain. The organization's outbound auto-replies had DKIM: none and DMARC: none on their domain. Implement DKIM signing for all outbound mail and set your DMARC policy to p=quarantine or p=reject. This does not prevent the inbound attack, but it prevents attackers from spoofing your domain in turn.
- Extend mobile device URL filtering. QR code phishing specifically targets mobile devices to bypass endpoint protection. Ensure MDM-enrolled devices have web filtering that covers known-malicious domains, and evaluate whether corporate-managed mobile browsers apply the same proxy and filtering rules as corporate workstations.
- Restrict auto-reply rules for external recipients. Consider disabling automatic external replies for accounts, or at minimum suppressing replies to domains not in your trusted partner list. The operational inconvenience is modest; the reconnaissance value to an attacker is not.
- Conduct targeted quishing awareness training. Train staff to treat QR codes in unsolicited emails with the same suspicion as hyperlinks. Emphasize that mobile devices do not benefit from the same email security protections as corporate workstations - scanning a QR code is equivalent to clicking a link on an unmanaged device.
- File abuse reports. Report to Namecheap (abuse@namecheap.com) for the hosting infrastructure at iconicdecipher[.]com and server182.web-hosting.com, and to Verizon FiOS (abuse@verizon.net) for the residential IP 71.105.63.133.
Conclusion
The attack documented here was not technically exotic. It did not exploit a zero-day, abuse a trusted platform, or require the victim to take any unusual action. It required them to scan a QR code - something people do without thinking, from devices that offer no protection.
What made it effective was the combination of proper authentication setup, a clean domain reputation, attachment-based URL encoding that is invisible to text-scanning tools, and mobile device delivery that sidesteps endpoint controls entirely. None of those elements is individually novel. Together, they constituted a campaign that bypassed every standard control and sat in 28 inboxes for days and possibly tens of thousands more in other environments.
The detection happened because of a different kind of coverage:AI agents that drove a structured investigation from alert to conclusion, an MDR analyst who noticed an anomaly, and a threat hunt that turned a single suspicious email into a full campaign map. That is what closed the gap.
Block the domains. Enable QR code scanning in your email security platform. Review your auto-reply rules. And be a little more suspicious of the next QR code that arrives in an unsolicited email.
About This Research
This research is based on an active quishing campaign investigation conducted by the 7AI threat research and security operations team, incorporating findings from 7AI PLAID ELITE monitoring, AI SOC investigation, and targeted threat hunting activity. All customer and organizational identifiers have been fully anonymized. No recipient names, email addresses, or organizational details appear in this report. Juliana Testa, Zack Nelson, August Moore, James Tufenkdjian, Erika Weiler, Tommy Scott, Evelyn Kim, Israel Bark, Yonatan Striem Amit, and Becca Barry were contributors to this in-depth research along with many others on the 7AI team.
IOCs in this report are confirmed from active investigations. Defenders are encouraged to operationalize them immediately.
For questions about this research or to share related findings, contact the 7AI threat research team at security@7ai.com.
Quish Splash FAQs
What is QR code phishing (quishing)?
QR code phishing, called "quishing," is a technique where attackers encode malicious URLs inside QR code images rather than placing links in the email body as text. Because traditional email security platforms scan text and HTML - not image pixel data - the URL is structurally invisible to standard link-scanning engines. The recipient is directed to an attacker-controlled page only after physically scanning the code with a mobile device, which typically lacks the endpoint protections of a corporate workstation.
Why did this quishing campaign bypass SPF, DKIM, and DMARC?
The attacker didn't bypass authentication - they passed it legitimately. They configured their domain with valid SPF, DKIM, and DMARC records, and used Namecheap shared hosting to send through an authorized mail relay. Microsoft EOP assigned a Spam Confidence Level of 1, the highest trust rating, and delivered the emails directly to inboxes. This is a deliberate attacker technique: proper DNS configuration removes the single signal most email gateways rely on to flag suspicious messages.
How does 7AI detect quishing attacks that bypass traditional email security?
7AI's AI SOC agents analyze inbound email attachments - including image files - to extract and evaluate embedded QR code content. By decoding the URL inside the image and correlating it against threat intelligence, 7AI identifies phishing activity that would otherwise be invisible to text-based inspection. In this investigation, the platform's true positive classification triggered a human escalation and threat hunt that uncovered the full campaign scope across all three waves and 32 recipients.
What should security teams do immediately if they receive a quishing email?
Block the sending domain and IP at your DNS resolver, perimeter firewall, and email gateway. Use Microsoft Defender's Search and Purge capability to remove delivered messages by sender and domain - do not rely on users to delete them manually. Contact every recipient and determine whether they scanned the QR code on a mobile device. Any recipient whose auto-reply reached the attacker should be treated as elevated-risk for follow-on spearphishing. Review outbound auto-reply transport rules to prevent reconnaissance leakage to external senders.
Why is hash-based IOC sharing ineffective against quishing campaigns?
In this campaign, every recipient received a uniquely generated QR code BMP file with a distinct SHA256 hash. A single file hash therefore cannot be shared as a blocking indicator across the campaign - by the time it's distributed, the attacker is already sending different files to the next organization. Effective blocking requires domain and URL-pattern-based controls, not file hashes.
Is QR code scanning in Microsoft Defender for Office 365 enabled by default?
No. Microsoft Defender has a feature to decode QR codes embedded in emails and attachments and detonate the resulting URLs, but it must be explicitly enabled in your anti-phishing policies. This is the single most effective technical control against quishing. Verify the setting in your tenant before the next campaign reaches your environment.
What is 7AI PLAID ELITE?
7AI PLAID ELITE is 7AI's managed security service - a People-Led, AI-Driven model that pairs 24/7 expert analyst coverage with the 7AI platform's AI SOC agents. In this investigation, PLAID ELITE analysts confirmed the phishing mechanism, escalated for a broader hunt, and worked with a 7AI AI Security Engineer to map the full campaign. It is the human layer that turns a true positive classification into an actionable intelligence picture.